IoT doorbell can reveal your Wi-Fi key
 Security researchers have discovered a glaring security hole that exposes the home network password of users of a Wi-Fi-enabled video doorbell. The issue underlines how default configurations of IoT components can introduce easy to exploit security holes.
Security researchers have discovered a glaring security hole that exposes the home network password of users of a Wi-Fi-enabled video doorbell. The issue underlines how default configurations of IoT components can introduce easy to exploit security holes.
The Ring allows punters to answer people knocking on your door from your mobile phone, even when you’re not at home. The kit acts as a CCTV camera, automatically activating if people approach your door, letting homeowners talk to visitors, delivery couriers and so on. There’s an optional feature that allows the kit to hook up to some smart door locks, so users can let guests into their home even when they aren’t in.
Read moreWhat technology will look like in five years
 As a driver of technical innovation for a software company, a huge part of my job depends on forecasting how current tech trends will play out, merge, dissipate or expand.
As a driver of technical innovation for a software company, a huge part of my job depends on forecasting how current tech trends will play out, merge, dissipate or expand.
Here are some of my predictions of what the world will look like in 2020. The notions of ownership will be revised. We’ve recently seen a huge rise in the sharing economy; not only can you stay in someone else’s house via Airbnb, but you can sail in someone else’s boat through Sailo, fly in someone else’s private plane via OpenAirplane and go snowboarding with someone’s else’s board via Spinlister. This is only the first wave.
Read moreCracking Wi-Fi passwords by hacking into smart kettles
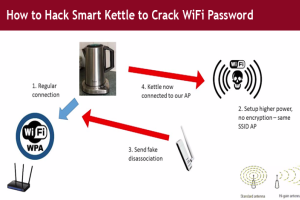 Hackers have come after your phone, your computer, and your car. Now hackers are coming after your home refrigerators, Smart TVs, and eventually KETTLES.
Hackers have come after your phone, your computer, and your car. Now hackers are coming after your home refrigerators, Smart TVs, and eventually KETTLES.
Yes, your kettle turns out good for more than just heating up water or making coffee for you– they are potentially a good way for hackers to breach your wireless network. A security researcher at PenTest Partners has managed to hack into an insecure iKettle and stolen a home's Wi-Fi password. Besides boiling water, the iKettle can connect to a user's home Wi-Fi network. It also comes inbuilt with an Android and iOS app that allows the user to switch on the kettle and boil the water from other location.
Read moreFather of the Internet is terrified of the Internet of Things
 Vint Cerf is known as a "father of the Internet," and like any good parent, he worries about his offspring -- most recently, the IoT. The Internet of Things will offer the ability to manage many of the appliances we depend on, acknowledged Cerf, who won the Turing Award in 2004.
Vint Cerf is known as a "father of the Internet," and like any good parent, he worries about his offspring -- most recently, the IoT. The Internet of Things will offer the ability to manage many of the appliances we depend on, acknowledged Cerf, who won the Turing Award in 2004.
With its ability to continuously monitor such devices, it also promises new insight into our use of resources, he said. As with so many technological tools, however, there are plenty of potential downsides. Safety is one of them. Cerf is now vice president and chief Internet evangelist at Google, but you won't find him enjoying any of the massage chairs the company provides for its employees.
Read moreInternet.org is not neutral, not secure, and not the Internet
 Facebook's Internet.org project, which offers people from developing countries free mobile access to selected websites, has been pitched as a philanthropic initiative to connect two thirds of the world who don’t yet have Internet access.
Facebook's Internet.org project, which offers people from developing countries free mobile access to selected websites, has been pitched as a philanthropic initiative to connect two thirds of the world who don’t yet have Internet access.
The global digital divide should be closed and we agree that some Internet access is better than none. However, we question whether this is the right way to do it. There's a real risk that the few websites that Facebook and its partners select for Internet.org could end up becoming a ghetto for poor users instead of a stepping stone to the larger Internet.
Read moreThe Internet of Things is very dangerous
 Owners of Internet-connected home security systems may not be the only ones monitoring their homes. A new HP study found that 100 percent of the studied devices used in home security contain significant vulnerabilities, including password security, encryption and authentication issues.
Owners of Internet-connected home security systems may not be the only ones monitoring their homes. A new HP study found that 100 percent of the studied devices used in home security contain significant vulnerabilities, including password security, encryption and authentication issues.
Home security systems, such as video cameras and motion detectors, have gained popularity as they have joined the booming Internet of Things market and have grown in convenience. Manufacturers are quickly bringing to market connected security systems that deliver remote monitoring capabilities.
Read moreMicrosoft considering public-key pinning for Internet Explorer
 Microsoft is considering adding public-key pinning–an important defense against man-in-the-middle attacks–to Internet Explorer. The feature is designed to help protect users against the types of MITM attacks that rely on forged certificates, which comprise a large portion of those attacks.
Microsoft is considering adding public-key pinning–an important defense against man-in-the-middle attacks–to Internet Explorer. The feature is designed to help protect users against the types of MITM attacks that rely on forged certificates, which comprise a large portion of those attacks.
Attackers use forged or stolen certificates to trick victims’ browsers into trusting a malicious site that the attacker controls. Public-key pinning helps prevent those attacks by binding a set of public keys issued by a trusted certificate authority to a specific domain. With that defense in place, if the user visits the site and is presented with a key that’s not part of the pinned set, the browser will reject the secure connection.
Read moreBillionaire’s next mission is Internet satellites
 Billionaire entrepreneur Elon Musk shook up the automotive and aerospace industries with electric cars and cheap rockets. Now, he is focused on satellites that can deliver Internet access across the globe, according to people familiar with the matter.
Billionaire entrepreneur Elon Musk shook up the automotive and aerospace industries with electric cars and cheap rockets. Now, he is focused on satellites that can deliver Internet access across the globe, according to people familiar with the matter.
Mr. Musk is working with Greg Wyler, a satellite-industry veteran and former Google Inc. executive. In talks with industry executives, Musk and Wyler have discussed launching satellites. They are considering building a factory to make satellites. Initial talks have been held with state officials about locating the factory. In addition to Mr. Musk, WorldVu is seeking a satellite industry partner to lend expertise to the project.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















